
Computer Stupidities
Moderators: Rebuild/OT Moderators, Board Staff
of course they do... it gets in the way of them trying to force everyone to use bing. 

Rest In Peace ~ 1978 - 2017
"I'd consider myself a realist, alright? but in philosophical terms I'm what's called a pessimist. It means I'm bad at parties." - Rust Cohle
"Think of how stupid the average person is, and realize that half of 'em are stupider than that." - George Carlin
"The internet: It's like a training camp for never amounting to anything." - Oglaf
"I think internet message boards and the like are dangerous." - Anno
"I'd consider myself a realist, alright? but in philosophical terms I'm what's called a pessimist. It means I'm bad at parties." - Rust Cohle
"Think of how stupid the average person is, and realize that half of 'em are stupider than that." - George Carlin
"The internet: It's like a training camp for never amounting to anything." - Oglaf
"I think internet message boards and the like are dangerous." - Anno
- pwhodges
- A Lilin in Wonderland

- Age: 77
- Posts: 11035
- Joined: Nov 18, 2012
- Location: Oxford, UK
- Contact:
I agree about Bing - but that's not comparable with messing with people's computers in an underhand way - which I say as the guy who gets to clean them up afterwards each time.
"Being human, having your health; that's what's important." (from: Magical Shopping Arcade Abenobashi )
"As long as we're all living, and as long as we're all having fun, that should do it, right?" (from: The Eccentric Family )
Avatar: The end of the journey (details); Past avatars.
Before 3.0+1.0 there was Afterwards... my post-Q Evangelion fanfic (discussion)
"As long as we're all living, and as long as we're all having fun, that should do it, right?" (from: The Eccentric Family )
Avatar: The end of the journey (details); Past avatars.
Before 3.0+1.0 there was Afterwards... my post-Q Evangelion fanfic (discussion)
- soul.assassin
- Geezer of All Trades

- Age: 47
- Posts: 4891
- Joined: Feb 26, 2010
- Location: Anywhere
- Gender: Male
- Shamsiel-kun
- Tokyo-3 Resident

- Posts: 1238
- Joined: Oct 09, 2014
- Location: Above/Below sea level
- Gender: Male
^ TBH, there's quite a few cases where IT personel itself are the idiots.
Case in point, I once overheard a IT worker at work give the following advice on passwords:
"It is best for your safety (in not forgetting passwords) that you use a single password all over the web, one that you can easily remember and that agrees with our password requirements (1 capital letter, 1 small letter, 1 punctuation mark, 8 chars mininum). But do not write it down."
He was not being sarcastic . I went away to get a coffee to avoid hearing the rest of the bullshit.
. I went away to get a coffee to avoid hearing the rest of the bullshit.
And last week I heard a numbnut explain how to transfer photos from a digital camera to Windows 7 and how to deal with slow computers ("The software that comes with a new computer is everything you need to use it. Manufacturers install all the programs you need in the most efficient* way possible and you get a free antivirus that you don't need to update because it always is up to date. When the computer gets slow, you should buy a new one**. Get one with at least a terabyte of memory***. I one had a 500 Gb harddisk that was full after I saved a few MS Word files to it****."). Now this one isn't an real IT guy, just an idiot who thinks he knows a lot about technology - he also believes airplanes can fly entirely on auto-pilot and don't need pilot input, ever .
.
* I guess he likes bloatware.
** The one discussed was bought last year.
*** He meant the hard disk.
**** ...and probably a crapton of porn.
Case in point, I once overheard a IT worker at work give the following advice on passwords:
"It is best for your safety (in not forgetting passwords) that you use a single password all over the web, one that you can easily remember and that agrees with our password requirements (1 capital letter, 1 small letter, 1 punctuation mark, 8 chars mininum). But do not write it down."
He was not being sarcastic
 . I went away to get a coffee to avoid hearing the rest of the bullshit.
. I went away to get a coffee to avoid hearing the rest of the bullshit.And last week I heard a numbnut explain how to transfer photos from a digital camera to Windows 7 and how to deal with slow computers ("The software that comes with a new computer is everything you need to use it. Manufacturers install all the programs you need in the most efficient* way possible and you get a free antivirus that you don't need to update because it always is up to date. When the computer gets slow, you should buy a new one**. Get one with at least a terabyte of memory***. I one had a 500 Gb harddisk that was full after I saved a few MS Word files to it****."). Now this one isn't an real IT guy, just an idiot who thinks he knows a lot about technology - he also believes airplanes can fly entirely on auto-pilot and don't need pilot input, ever
 .
.* I guess he likes bloatware.
** The one discussed was bought last year.
*** He meant the hard disk.
**** ...and probably a crapton of porn.
- Ornette
- Administrator

- Age: 49
- Posts: 11887
- Joined: Dec 26, 2005
- Location: Pittsburgh/New York City
- Gender: Male
- Contact:
There was actually a talk I saw last Dexember or so and another research paper that looked at password policies from a purely risk assessment standpoint. Some of the interesting takeaways was that using the ssame (but sufficiently strong) password everywhere isn't nearly as bad as people make it out to be. Some of the common problems with strict policies is that people can't remember that many passwords, and end up writing it down, putting then in a virtual post-it note, or emailing them to themselves or each other. Another aspect is that attack vectors these days (and over the last decade+, really) don't ever use stolen passwords, as those are mostly personal targets as opposed to a company or organization. Ocerwhelmingly, companies and organizatiinal IT security staff deal with intrusion through misconfiguration, bugs in software, and malware, and the targets are usually data breaches, not one specific guy who happened to use the ssame passwords for some other site that was involved with another data breach.
This is not to say that having good password policies is useless, any administrator should have really sstrong policies, but it can actually hurt the organizational infosec to have strlct policies for regular users. And of course, it has to do with what organizations and rhe size. Having differrnt passwords still good policy in general for personal infosec, but theres evidence that its not nearly as big a dedeal as its been made out to be in IT.
I'm on my phone rright now so digging up the papers not easy to do, can't remember tthe security conference the talk was from, it may have been OWASP related.
This is not to say that having good password policies is useless, any administrator should have really sstrong policies, but it can actually hurt the organizational infosec to have strlct policies for regular users. And of course, it has to do with what organizations and rhe size. Having differrnt passwords still good policy in general for personal infosec, but theres evidence that its not nearly as big a dedeal as its been made out to be in IT.
I'm on my phone rright now so digging up the papers not easy to do, can't remember tthe security conference the talk was from, it may have been OWASP related.
- Shamsiel-kun
- Tokyo-3 Resident

- Posts: 1238
- Joined: Oct 09, 2014
- Location: Above/Below sea level
- Gender: Male
Ornette wrote:There was actually a talk I saw last Dexember or so and another research paper that looked at password policies from a purely risk assessment standpoint. Some of the interesting takeaways was that using the ssame (but sufficiently strong) password everywhere isn't nearly as bad as people make it out to be.
(bolding mine)
In this case the person was having trouble remembering something as simple as "Poodle123$" - and also has fallen prey to phishing several times already despite having had at least one stern (and public) talk about it. Not going to end well if he uses a single password for all his stuff.
Personally I write down my passwords on a piece of paper (without the username next to it) and keep it somewhere safe. Hackers would have to physically break into my places to find the password...
- Ornette
- Administrator

- Age: 49
- Posts: 11887
- Joined: Dec 26, 2005
- Location: Pittsburgh/New York City
- Gender: Male
- Contact:
"Poodle123$" is more than sufficiently strong. The thing is, the original reason to make passwords contain numbers and capital letters is so they're hard to guess. If you make them too complicated, the average Joe is going to have to write it down somewhere, and the problem is made geometrically worse by having them choose a different one for every site they visit. Most people still aren't savvy enough to use password managers or 2-factor auth. Most sites have a "good enough" password policy built into the application, that you can say, "Poodle123$" is more than good enough, because brute force attacks get trapped and blocked. If this was your banking site or credit card site or something, you may even get an email saying someone just tried to log in and failed 5 times. The point is to choose a password that's not "password1" or "abcd1234" that someone can remember. Like I mentioned before, malware makes up a large portion of how attacks are carried out, and while brute force dictionary attacks are still commonplace, they're just not even remotely effective in comparison. And the thing with malware? They log your keystrokes and peek into your paste buffer, so you can have a password thats 100 characters long and it wouldn't matter. If you were sophisticated enough to install a password manager that injects the password into forms or other applications, you're probably not in the group of "average Joe" users that can't remember complicated passwords anyways.
As far as phishing, it's a battle that simply can't be won. Some friends of mine works for a security firm that assesses phishing risks for other companies and one of the things they do is launch some out-of-the-box phishing emails, after their employees were given a short tutorial on what phishing emails may look like and to general "be careful what you click on". Across the board, in every field they've worked with, the average click rate (these are the percentages of people who clicked on a phishing test email after the tutorial) is about %50 to %80 percent. With that kind of risk, telling these people to choose a password that is more than their dog's name is really not making much of a dent given what the attack vectors are. Additionally, people can get you to click on a phishing link no matter how good you are, even if you verify every link with curl/wget that you see in any email you get. Everyone in the security industry knows that with enough personal info that can be found about someone, eventually, they could be susceptible to clicking on a link that they shouldn't have, no matter how savvy they think they are. Someone who's deter,mined enough will eventually catch you off guard and an email from your best friend that actually continues the conversation that you were just having with him/her could direct you to a link and without thinking, you click on it.
As far as phishing, it's a battle that simply can't be won. Some friends of mine works for a security firm that assesses phishing risks for other companies and one of the things they do is launch some out-of-the-box phishing emails, after their employees were given a short tutorial on what phishing emails may look like and to general "be careful what you click on". Across the board, in every field they've worked with, the average click rate (these are the percentages of people who clicked on a phishing test email after the tutorial) is about %50 to %80 percent. With that kind of risk, telling these people to choose a password that is more than their dog's name is really not making much of a dent given what the attack vectors are. Additionally, people can get you to click on a phishing link no matter how good you are, even if you verify every link with curl/wget that you see in any email you get. Everyone in the security industry knows that with enough personal info that can be found about someone, eventually, they could be susceptible to clicking on a link that they shouldn't have, no matter how savvy they think they are. Someone who's deter,mined enough will eventually catch you off guard and an email from your best friend that actually continues the conversation that you were just having with him/her could direct you to a link and without thinking, you click on it.
For the record, I practice the below and store my secrets in pass.
Given how many websites don't store passwords safely, are likely to be breached, and don't perform proper rate-limiting on brute-force password attacks*, the best practice for passwords is clearly as follows:
0) Only memorize one password -- a master password that is used to unlock a password manager. Keep backups of this password manager. Ideally, the password manager should be totally offline.
1) Never write down any of your passwords.
2) Use a different, long, randomly-generated password for every site. "Long" in this case means 20 characters or more of quality random data, if the site will allow you to.
This way, when companies' password stores are inevitably breached, the damage is contained to that one website.
Oh, and:
3) If you're in a technical position, learn and talk up alternative means of authentication, such as public-key auth, that don't put as much of a burden on the end-user. It's embarrassing how many so-called software engineers don't understand what public-key cryptography can do -- it doesn't even require any math to understand that part.
* EvaGeeks Forums is probably guilty of at least two of those three things. We don't even have proper HTTPS, so for most of you, if you access EGF from Starbucks, an attacker could easily steal your current session tokens, at a minimum.
Given how many websites don't store passwords safely, are likely to be breached, and don't perform proper rate-limiting on brute-force password attacks*, the best practice for passwords is clearly as follows:
0) Only memorize one password -- a master password that is used to unlock a password manager. Keep backups of this password manager. Ideally, the password manager should be totally offline.
1) Never write down any of your passwords.
2) Use a different, long, randomly-generated password for every site. "Long" in this case means 20 characters or more of quality random data, if the site will allow you to.
This way, when companies' password stores are inevitably breached, the damage is contained to that one website.
Oh, and:
3) If you're in a technical position, learn and talk up alternative means of authentication, such as public-key auth, that don't put as much of a burden on the end-user. It's embarrassing how many so-called software engineers don't understand what public-key cryptography can do -- it doesn't even require any math to understand that part.
* EvaGeeks Forums is probably guilty of at least two of those three things. We don't even have proper HTTPS, so for most of you, if you access EGF from Starbucks, an attacker could easily steal your current session tokens, at a minimum.
- Mr. Tines
- Administrator

- Age: 66
- Posts: 21376
- Joined: Nov 23, 2004
- Location: This sceptered isle.
- Gender: Male
- Contact:
https://www.schneier.com/blog/archives/2005/06/write_down_your.html
Reminder: Play nicely <<>> My vanity publishing:- NGE|blog|Photos|retro-blog|Fanfics &c.|MAL|𝕏|🐸|🦣
Avatar: art deco Asuka
Avatar: art deco Asuka
- pwhodges
- A Lilin in Wonderland

- Age: 77
- Posts: 11035
- Joined: Nov 18, 2012
- Location: Oxford, UK
- Contact:
Complexity is a stupid way to make good passwords - that's what makes them hard to remember, and it was only necessary because of the old Unix limitation to a maximum length of 8 characters.
My user password policy is based on a number of papers from different places, and is very simple: no less than fourteen characters - and that's it, not even forced changes. Any phrase you fancy, as easy to remember as you like; if you have a "favourite" password you want to reuse, just type it twice if it's not long enough. Mind you, my admin password is nineteen characters and somewhat complex, naturally!
My user password policy is based on a number of papers from different places, and is very simple: no less than fourteen characters - and that's it, not even forced changes. Any phrase you fancy, as easy to remember as you like; if you have a "favourite" password you want to reuse, just type it twice if it's not long enough. Mind you, my admin password is nineteen characters and somewhat complex, naturally!
"Being human, having your health; that's what's important." (from: Magical Shopping Arcade Abenobashi )
"As long as we're all living, and as long as we're all having fun, that should do it, right?" (from: The Eccentric Family )
Avatar: The end of the journey (details); Past avatars.
Before 3.0+1.0 there was Afterwards... my post-Q Evangelion fanfic (discussion)
"As long as we're all living, and as long as we're all having fun, that should do it, right?" (from: The Eccentric Family )
Avatar: The end of the journey (details); Past avatars.
Before 3.0+1.0 there was Afterwards... my post-Q Evangelion fanfic (discussion)
FWIW the advice I gave above is easily compatible with this: write down your master password and keep the rest in a password store ("written down" digitally). That's honestly more what I was thinking about.
Just consider very carefully before using a cloud password-store provider like LastPass.
I know determining password entropy is difficult to do, but do you at least prevent runs of "aaaa" or similar?
- soul.assassin
- Geezer of All Trades

- Age: 47
- Posts: 4891
- Joined: Feb 26, 2010
- Location: Anywhere
- Gender: Male
- pwhodges
- A Lilin in Wonderland

- Age: 77
- Posts: 11035
- Joined: Nov 18, 2012
- Location: Oxford, UK
- Contact:
I prevent runs, keyboard layout (qwerty, etc), reuse of user name - the last of these is the only one I've ever seen tripped by a user's first choice.
-----------------------------------------------------------------------------------------------------------------
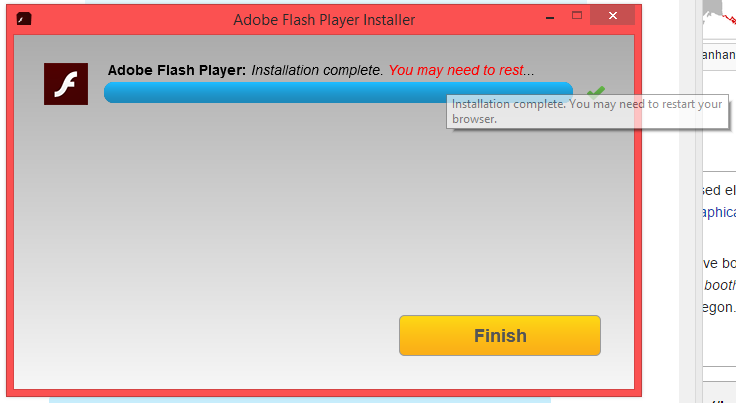
I needed to install Flash. I like how tiring the installer found it (until I hovered over it):
"Being human, having your health; that's what's important." (from: Magical Shopping Arcade Abenobashi )
"As long as we're all living, and as long as we're all having fun, that should do it, right?" (from: The Eccentric Family )
Avatar: The end of the journey (details); Past avatars.
Before 3.0+1.0 there was Afterwards... my post-Q Evangelion fanfic (discussion)
"As long as we're all living, and as long as we're all having fun, that should do it, right?" (from: The Eccentric Family )
Avatar: The end of the journey (details); Past avatars.
Before 3.0+1.0 there was Afterwards... my post-Q Evangelion fanfic (discussion)
- Shamsiel-kun
- Tokyo-3 Resident

- Posts: 1238
- Joined: Oct 09, 2014
- Location: Above/Below sea level
- Gender: Male
^ The big security hole that is now exploited in the wild after that hack of that spyware maker (hilarious event, by the way...  ) made me panic for a moment, until I reminded myself that I didn't bother to install flash on my Windows machine in the first place (nor did I install Java...).
) made me panic for a moment, until I reminded myself that I didn't bother to install flash on my Windows machine in the first place (nor did I install Java...).
That just leaves my ancient laptop that I use to browse the web. Anyone know whether that security hole affects Shockwave Flash version 9.something on PowerPC Macs?
 ) made me panic for a moment, until I reminded myself that I didn't bother to install flash on my Windows machine in the first place (nor did I install Java...).
) made me panic for a moment, until I reminded myself that I didn't bother to install flash on my Windows machine in the first place (nor did I install Java...).That just leaves my ancient laptop that I use to browse the web. Anyone know whether that security hole affects Shockwave Flash version 9.something on PowerPC Macs?

- soul.assassin
- Geezer of All Trades

- Age: 47
- Posts: 4891
- Joined: Feb 26, 2010
- Location: Anywhere
- Gender: Male
- pwhodges
- A Lilin in Wonderland

- Age: 77
- Posts: 11035
- Joined: Nov 18, 2012
- Location: Oxford, UK
- Contact:
I did my first upgrade to Windows 10 last night. Nothing much to say yet, as I haven't done anything with it - but it worked.
However, a colleague had a bit of trouble. This was, of course, reported meticulously by the Windows 10 installer with two successive messages:
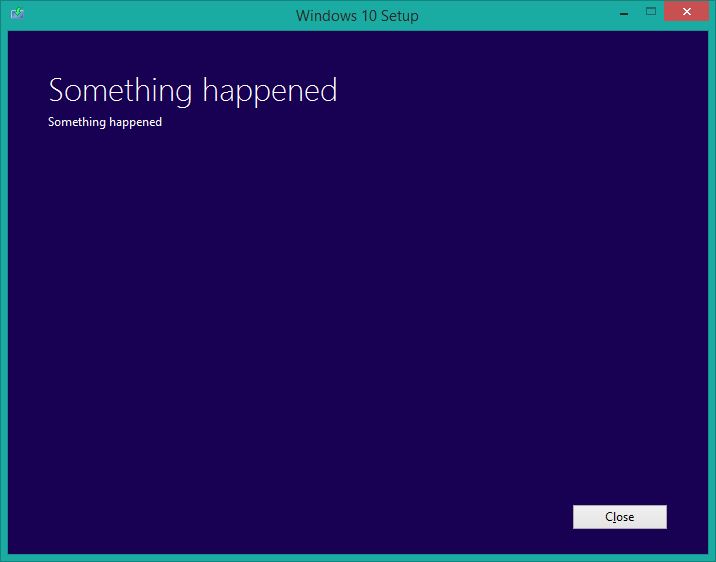
However, a colleague had a bit of trouble. This was, of course, reported meticulously by the Windows 10 installer with two successive messages:
"Being human, having your health; that's what's important." (from: Magical Shopping Arcade Abenobashi )
"As long as we're all living, and as long as we're all having fun, that should do it, right?" (from: The Eccentric Family )
Avatar: The end of the journey (details); Past avatars.
Before 3.0+1.0 there was Afterwards... my post-Q Evangelion fanfic (discussion)
"As long as we're all living, and as long as we're all having fun, that should do it, right?" (from: The Eccentric Family )
Avatar: The end of the journey (details); Past avatars.
Before 3.0+1.0 there was Afterwards... my post-Q Evangelion fanfic (discussion)
- soul.assassin
- Geezer of All Trades

- Age: 47
- Posts: 4891
- Joined: Feb 26, 2010
- Location: Anywhere
- Gender: Male
- pwhodges
- A Lilin in Wonderland

- Age: 77
- Posts: 11035
- Joined: Nov 18, 2012
- Location: Oxford, UK
- Contact:
Previous contents of post - SPOILER: Show
How about:

or this:
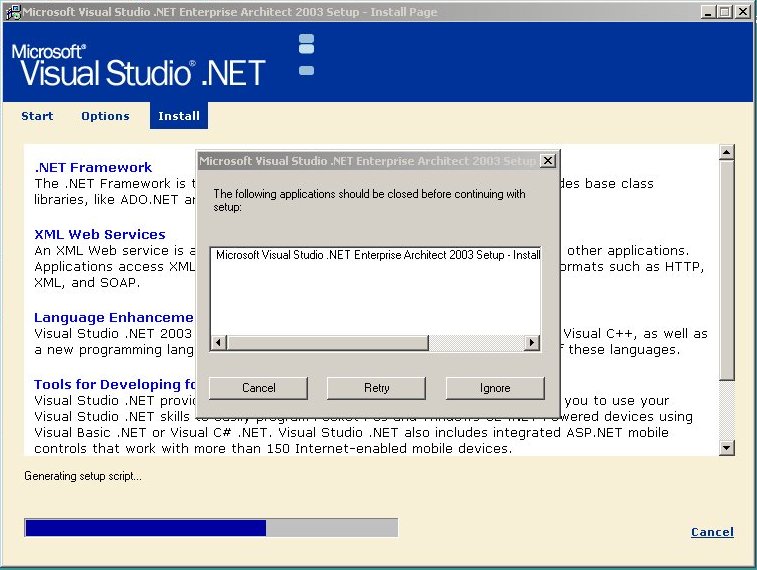

or this:
--------------------------------------------------------------------------------------------------------------

Windows 10 by default torrents its updates, meaning that it is using your upload bandwidth for the purpose without your permission.
[url]http://thehackernews.com/2015/08/windows-10-update.html[/url]
"Being human, having your health; that's what's important." (from: Magical Shopping Arcade Abenobashi )
"As long as we're all living, and as long as we're all having fun, that should do it, right?" (from: The Eccentric Family )
Avatar: The end of the journey (details); Past avatars.
Before 3.0+1.0 there was Afterwards... my post-Q Evangelion fanfic (discussion)
"As long as we're all living, and as long as we're all having fun, that should do it, right?" (from: The Eccentric Family )
Avatar: The end of the journey (details); Past avatars.
Before 3.0+1.0 there was Afterwards... my post-Q Evangelion fanfic (discussion)
- Sicarius VI
- Tokyo-3 Resident

- Age: 25
- Posts: 1149
- Joined: Aug 12, 2014
- Location: United States
- Gender: Male
Return to “Completely and Utterly Off-Topic”
Who is online
Users browsing this forum: No registered users and 39 guests


